4 Ways to Conduct Security Rounds
No two facilities’ operations are identical. Each of their standards, goals, and procedures makes them unique. However, there is one thing that all facilities have in common: conducting security rounds.
Security rounds are arguably the most important duty a correctional officer can perform. This isn't just because it’s a way to simultaneously conduct headcount while confirming that inmates are where they should be, but because it’s how you ensure the well-being of the inmates.
Officers should never conduct their security rounds while distracted to avoid missing key warning signs or potential concerns. Physically assessing an individual or situation helps gauge the environment and obtain useful information that can detect and prevent emergencies. Maintaining the safety and security of the inmates in their custody is the utmost responsibility of any correctional officer.
In this blog, we break down four ways to conduct security rounds, along with their pros and cons, so that facilities can determine which method they should implement within their facility.
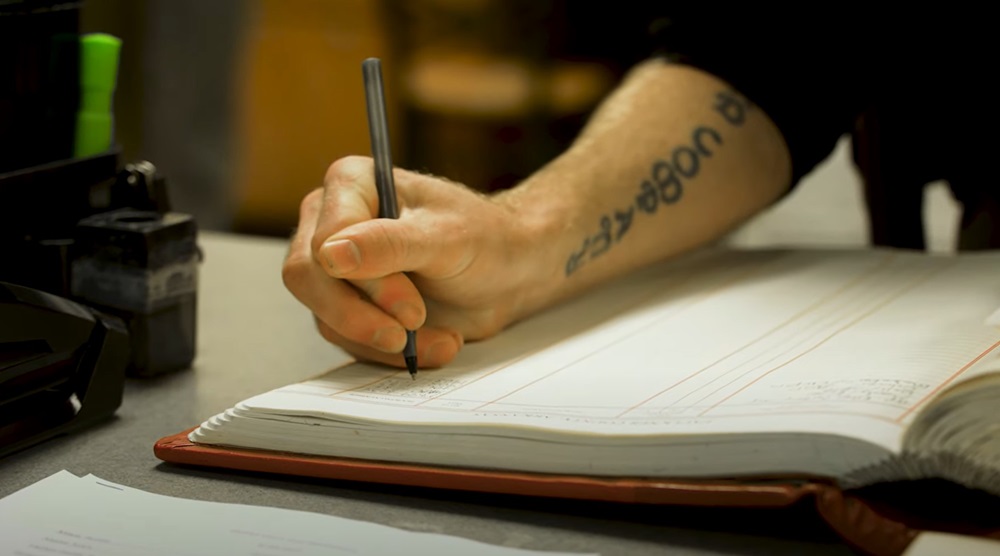
Good Ole’ Fashioned Pen and Paper
Let’s start with the most prehistoric data-logging method: pen and paper.
This manual method, of course, is the most traditional way of documenting inmate activity, behaviors, and movement. It’s “unbreakable”. It’s more accessible. It’s cheaper. It’s easier.
We all know and understand the budget restraints that hinder facilities from adopting newer, advanced methods. Sadly, it’s a reality for many correctional facilities with limited funding. This reality has made the terms “budget-friendly” and “easy to use”, two of the biggest selling points for paper logs.
Most facilities have used paper logs at one point or another, making it a familiar method for staff. However, just because staff are comfortable with something, doesn’t mean it's the best option. The staff who are set in their ways are typically the same ones who live by the phrase we’ve all heard before, “If it’s not broken why fix it?”
But the fact is, there are risks that come with this method. Long story short, the two biggest concerns with using manual documentation are efficiency and accuracy.
To put it simply, paper logs are not time-efficient. Whether it’s the time it takes to manually write out notes and observations or sorting through years upon years of paperwork in the shed out back, there is no quick or simple way of completing or locating critical documentation.
Say you’re conducting rounds and think, “Hmm, I need to write that down when I am done with checks.” This leaves ample opportunity to forget, get distracted, or misconstrue what you meant to document. Being a correctional officer is no easy job with bountiful free time. You’re inevitably going to get distracted or off-track with the seemingly million responsibilities you have.
Written notes can also cause an issue with the accuracy of your documentation. The time or comments can be recorded incorrectly or inaccurately with no substantial proof. While you want to believe all paper logs are accurate, officers could inaccurately record activities just to meet compliance requirements. That is if you can even read the written notes at all…
The cons of pen and paper have led agencies to explore more efficient and accurate data-capturing options, such as adopting technology.
RFID or NFC Readers
Thanks to our smartphones, nearly all of us have become accustomed to having the power of technology at our fingertips. With just a few clicks of a button, we can search and access almost anything. Luckily for us, this plethora of capabilities on our smartphones can extend to the corrections industry.
Similarly to how you scan the barcode of a ticket on your phone to enter a football game, our phones can be used to scan RFID (Radio Frequency Identification) or NFC (Near Field Communication) readers. This allows officers to complete security rounds more efficiently and accurately.
Both of these wireless readers can be encrypted inside a tag placed on the outside of each cell door. This accessibility allows officers to easily scan the tag while looking into the cell to document their observations. There are a variety of reasons why agencies favor this method of data collection, but the most significant is the built-in security and risk mitigation features that ensure data protection. Facilities can accomplish this by using:
Authentication: NFC and RFID user authentication protocols validate device communication, ensuring that only authorized devices can exchange information, and preventing unauthorized access.
Encryption: Safeguard sensitive data during transmission by employing encryption algorithms to help protect against eavesdropping and unauthorized tampering, thus ensuring secure communication channels.
Access controls: NFC and RFID systems can implement access controls such as passwords or biometrics to restrict unauthorized usage. These measures add another layer of security ensuring only authorized individuals can interact with the technology.
This method seems like a strong option considering all the pros, right? While that may be true, it’s important to note that RFID and NFC data-collection systems usually come with a price tag. But, that’s what happens when you pay for quality, right? Especially considering how reliable the data would be in the event of litigation. For facilities that regularly experience inmate complaints, this technology could actually save them money in the future.
The functionality is there if the budget is available. While this is an efficient and effective way to conduct security rounds, its associated up-front cost is primarily why many agencies opt for a less reliable, cheaper option.
Guard Tour Systems
Another technology used within jails and prisons is guard tour systems. These systems are used to monitor and record the activity of security guards or patrol officers as they make their rounds at different checkpoints and locations. Guard tour systems typically have some type of electronic network of sensors installed at designated checkpoints. These systems record the time and location of each checkpoint scanned, providing a detailed record of the guard’s movements and activities during their shift.
The guard tour concept was introduced to North America in the 1980s as a tool to advance the security round process. Instead of using pen and paper to track rounds, officers could simply scan a checkpoint to document that a check was completed - which was riveting technology for the industry in the late 80s and early 90s.
Guard tour systems are used in many industries where security needs to be closely monitored, including factories, warehouses, schools, hospitals, banks, and military institutions. Hence, why it eventually migrated to correctional facilities.
In correctional facilities, specifically, checkpoints would be strategically installed at key areas in a facility that needed monitoring. This included pod doors, entry and exit points, the booking area, and more. Officers would carry a handheld device equipped with the software needed to scan and record their movements at each checkpoint. The data collected by the device would transmit in real-time or at scheduled intervals depending on the cloud-based server.

The ability to quickly scan a checkpoint and document that a check was completed drastically lowered the time spent during security rounds. This method enhanced officer accountability, improved security, and increased efficiency with officer activities. However, guard tour systems reached the height of their popularity in the late 90s and early 2000s. Not long after its widespread hype, more risks became apparent.
The biggest challenges associated with guard tour systems were, and still are:
Technical malfunctions: Many users experience daily device failures and glitches, disrupting the effectiveness of the product as well as compromising its reliability.
Vulnerability to tampering: Guard tour systems can be easily tampered with. While users should uphold the oath they took on their badge, there are still unfortunately some bad eggs out there that will falsify reports and data to cover up the gaps in their duties. The security documentation method itself isn’t strong enough to avoid manipulation.
Limited coverage: Initially designed to specifically monitor checkpoints, guard tour systems don’t provide coverage of an entire facility. This presents a major lack of awareness in areas that should be monitored (especially if inmates know they aren’t being monitored!)
Data collection: Given the manual process of collecting data, not all captured information provides meaningful insights to communicate with an agency’s jail management system (JMS). This requires more labor and time to be put towards physical data entry, organization, and validation.
Detail-restrictive: While you can see when security rounds were completed, officers can’t document what was observed. This is especially damaging when it comes to legal defensibility. If an officer’s compliance (or job) ever comes into question, not having solid proof can quickly become a wicked game of he said, she said.
The various challenges that users experience with guard tour systems often force them to turn back to pen and paper to document security rounds (and that's when you really know you have a problem).
Staff that experience the switch back to paper logs from a guard tour system are normally frustrated and left questioning the technology investment in the first place. And how could you blame them? What’s the point of investing in technology if you have to juggle different tools to document your security rounds? Technology is meant to cut back the need for ineffective methods, not use multiple tools to accomplish one responsibility.
It’s the outdated and unreliable methods like guard tour systems that unfortunately give technology options in corrections a bad reputation. However, just because the guard tour method lacks the critical elements that promote extensive and efficient security rounds, doesn’t mean that all technology options fall short.
The Officer Experience Platform
The most recent industry breakthrough catching the attention of agencies across the country is the Officer Experience Platform (OXP).
The OXP, Command Cloud, was launched in 2023 by GUARDIAN RFID. Since then, it has proven to be a revolutionary tool in changing correctional operations in facilities nationwide. It was built for all correctional facilities, including county jails, juvenile detention centers, prisons, and federal detention centers.
As the name, “Officer Experience,” suggests, this platform was built specifically with correctional officers in mind. Command Cloud combines data from traditionally disparate systems to provide context, allowing officers to execute decisions quickly with higher situational awareness and quick collaboration. It leverages new and existing cameras, RFID, and vision systems, and will integrate with more than 80 different applications. Some of these applications include offender, jail, and case management systems.
Command Cloud addresses common challenges within correctional facilities such as:
AWARENESS: OXPs create safer environments for monitoring specific threats by automatically identifying human movements, behaviors, and other assets of inmates happening in real-time. Officers can be alerted to manage and track the designated groups or items in their approved locations, such as workshop tools or kitchen equipment.
COLLABORATION: OXPs connect people and systems to drive collaboration, insights, and learning in the flow of work. Working as a team on a shared objective by using task-driven responsibility and effective communication allows officers to quickly provide status updates or request assistance or intervention if needed.
INSIGHT: OXPs identify and measure areas of performance. Understanding what’s happening (or has happened) based on historical patterns and decisions, whether good or bad, helps agencies identify gaps or areas for improvement and prioritization.
DISCOVERABILITY: OXPs improve safety and security by collecting data from separate jail operating systems to narrow down results. This includes the use of the search bar, group by cards, filters, and broad terms to find what you’re looking for.
While secure data capture was only one of the factors considered when building this technology platform, it’s the most powerful method of conducting security rounds. Plus, Command Cloud is a cloud-based platform paired with ruggedized mobile devices and can be easily deployed and up and running within days.
Deploying GUARDIAN RFID underscores the department’s strong commitment to the safety and security of our employees. Command Cloud will enhance staff safety, boost efficiency in daily tasks, and ultimately elevate the quality of services provided to our residents. The New Hampshire Department of Corrections is excited to be a part of shaping the future of corrections technology.
Commissioner Helen HanksNew Hampshire Department of Corrections
It’s important to note that with these advantages, there’s a possibility that an OXP may be a little overkill for your facility’s specific needs. For example, if your agency is searching for a system for only conducting rounds, an OXP would carry too many bells and whistles for that task alone.
An OXP goes above and beyond by tracking supplies, movements, headcounts, meals, recreation time, and so much more. However, if an agency that only wants to conduct rounds also wants to track compliance percentages, then an OXP would be a good option for them to explore. And if that’s the case, the only hindering factor of Command Cloud as an OXP option is whether it fits inside the facility’s budget.
When it’s all said and done, purchasing the hardware, software licenses, maintenance, installation, and training can add up and be expensive for some agencies. And GUARDIAN RFID understands that. That’s why there are finance programs or special offerings set in place to allow agencies to modernize their facility operations without stressing about costs.
It doesn’t cost anything to be diligent and secure when capturing critical data during security rounds. Adopting and embracing technology built to enhance the accuracy, efficiency, and effectiveness of the officer's responsibilities at hand is priceless.
In fact, approximately 85% of new Command Cloud users reach around 90% compliance or higher within the first 90 days of implementing the system.
Powerful technology will always be more reliable than pen and paper and lagging guard tour systems. As technology innovation continues to advance, so do the responsibilities of agencies to invest wisely. It’s imperative for administrators to carefully evaluate which methods best align with their facility’s unique operations, goals, and needs.
The journey to optimizing security rounds is a multifaceted one. By staying informed, adaptable, and committed to leveraging the best tools available, agencies can strive towards creating safer and more secure environments in their facilities.

